How to Automatically Enroll Active Directory devices in Intune using Group Policy. (Microsoft 365).
In this guide you'll learn how you can enroll on-premises Active Directory (AD) domain-joined devices to Intune to centralize manage them.
If your on-premises Active Directory is integrated with Microsoft Entra ID (via Microsoft Entra Connect), managing multiple Windows devices is much easier when they are automatically enrolled in Microsoft Intune.
With MDM Auto-Enrollment, users in your domain will sign in to their Windows PC with their Microsoft 365 corporate account and their device will automatically be enrolled in Intune for centralized management.
How to Enroll Active Directory (AD) Windows devices to Intune Automatically.
Perquisite: Your on-premises AD is already synchronized to Microsoft Entra ID with Microsoft Entra Connect (aka "Azure AD Connect").
Step 1. Enable automatic MDM enrolment using default Azure credentials in Group Policy.
1. On the Server Manager, go to Tools and open the Group Policy Management.
2. Create a new Group Policy Object (GPO) and link it to your domain or to the organizational unit (OU) that contains the users and/or devices you want to synchronize with Microsoft Entra ID.
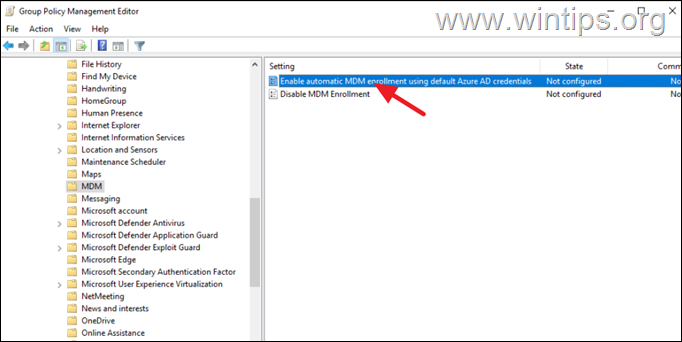
3. Open (Edit) the new Group Policy Management Editor, and navigate to:
- Computer Configuration > Administrative Templates > Windows Components > MDM
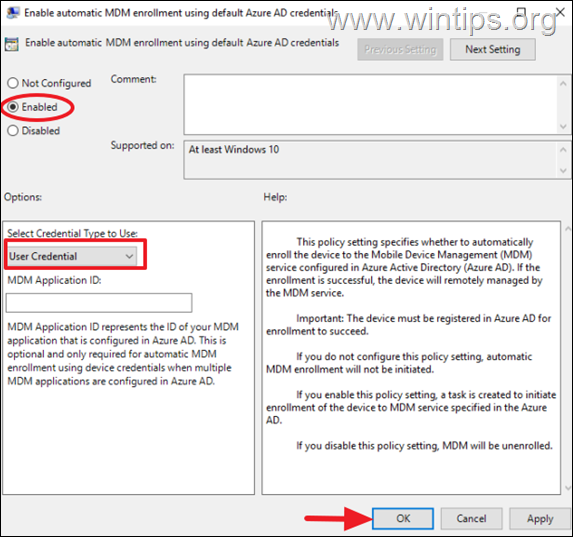
4. Open Enable automatic MDM enrolment using default Azure AD credentials policy.*
* Note: If the "Enable automatic MDM enrolment using default Azure credentials" policy is missing, see the instructions below how to add it.
5. Set the policy to Enabled and below select User Credential as the credential type to use for enrollment. Click Apply > OK and then close the group policy editor.
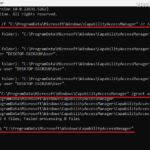
6. Run the "gpupdate /force" command to apply the policy and continue to step-2.
How to Add the "Enable automatic MDM enrolment using default Azure AD credentials" policy if it is missing.
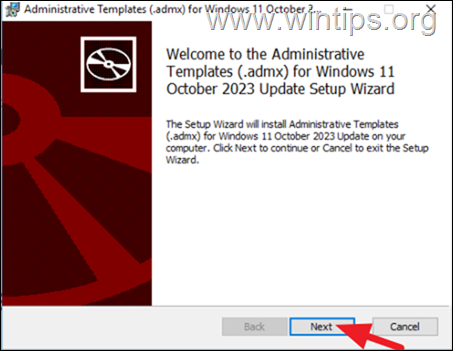
1. According to the latest Windows version installed on the domain workstations, download the Administrative Templates (.admx) package from the below links:
- Windows 11, version 25H2
- Windows 11, version 24H2
- Windows 11, version 23H2
- Windows 11, version 22H2
- Windows 10, version 22H2
2. Then install the downloaded package on the Domain Controller.
3. After installation, navigate to the path where the ADMX templates are installed.*
* eg. If you installed the "Windows 11 (23H2)" admx templates, navigate to:
- C:\Program Files (x86)\Microsoft Group Policy\Windows 11 October 2023 Update (23H2)\
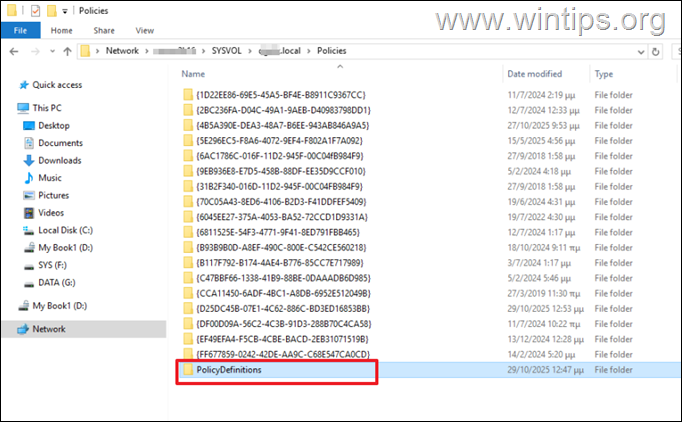
4. Copy the "PolicyDefinitions" folder to the following location:
5. When done, wait for the SYSVOL DFSR replication to be completed (this takes about ~15 seconds for domain controllers that are in the same site) and then follow the instructions on step-1 above to enable the automatic MDM enrollment.
Step 2. Enable Automatic Enrollment in Microsoft iTune Admin Center.
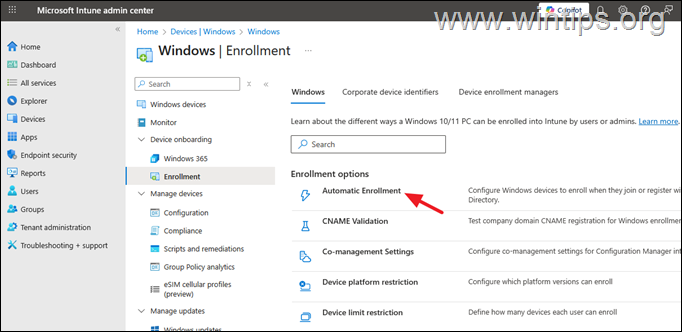
1. Navigate to Intune Admin Center > Devices > Windows > Enrollment and open Automatic Enrollment.
2. Set the MDM user scope to All and the Windows information Protection (WIP) to All* and click Save.*
* Note: If during the enrollment of a Windows device (step-3), you receive the error "Device Management could not be enabled" with "Error code: -2145833241 or 80192EE7", then set the Windows information Protection (WIP) to None and try again to enroll the device.
Step 3. Verify Device Enrollment in Intune.
After performing the above actions, on any Windows device that is synchronized with the Microsoft Entra ID (via "Azure AD Connect" tool), users will be prompted to enter their Microsoft 35 credentials to enroll their device in Microsoft Intune.
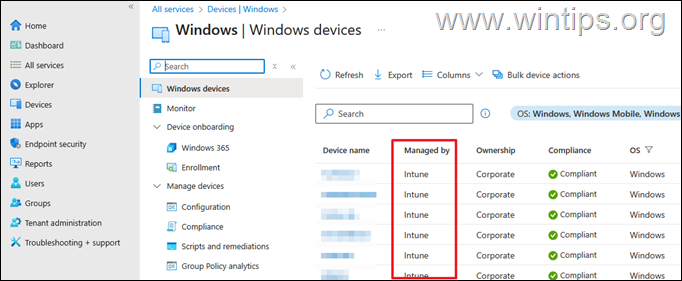
Therefore, wait until the Azure AD synchronization service to run again, and after the synchronization, navigate to Intune Admin Center > Devices > Windows Devices to verify that the device is enrolled and managed by Intune.
Additional Help:
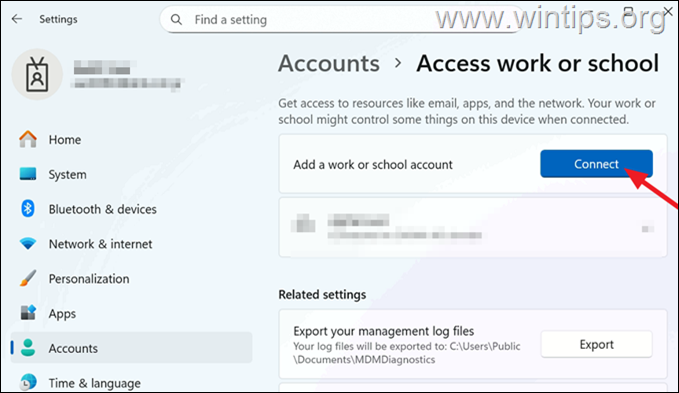
1. To enroll a Windows 11/10 device manually in Intune:
Go to Settings > Accounts > Access work or School and next to Add a work or school account click Connect. Then enter the Microsoft 365 account credentials to enroll the device in Intune.
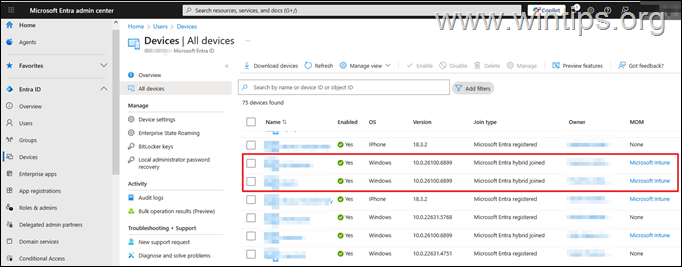
2. If a device is already register in Microsoft Entra before the synchronization, normally after the synchronization will shown as "Microsoft Entra hybrid joined" device.
If this does not happen, and you see the device still listed as "Microsoft Entra registered" or listed twice in Microsoft Entra ID (once as "Registered" and once as "Hybrid joined"), then do the following on the affected workstation:
1. Open Command Prompt as Administrator and give the below command:
- dsregcmd.exe /leave
2. Restart the computer and then add your work or school account again.
That's it! Let me know if this guide has helped you by leaving your comment about your experience. Please like and share this guide to help others.
Frequently Asked Questions
What is the prerequisite for enrolling on-premises AD devices to Intune automatically?
Your on-premises Active Directory must be synchronized to Microsoft Entra ID using Microsoft Entra Connect (aka 'Azure AD Connect').
How can I enable automatic MDM enrollment for Windows devices?
Use Group Policy Management to create and configure a new Group Policy Object with the 'Enable automatic MDM enrolment using default Azure AD credentials' policy, setting it to Enabled with User Credential as the credential type for enrollment, then apply the policy.
What should I do if the 'Enable automatic MDM enrolment using default Azure credentials' policy is missing?
Download and install the latest Administrative Templates (.admx) package according to the Windows version on the domain workstations, then copy the 'PolicyDefinitions' folder to the appropriate SYSVOL location on your domain controller.
How can I verify that a Windows device is enrolled in Intune?
After enabling automatic enrollment and syncing with Microsoft Entra ID, navigate to Intune Admin Center > Devices > Windows Devices to confirm that the device is enrolled and managed by Intune.

![image_thumb[10] image_thumb[10]](https://www.wintips.org/wp-content/uploads/2025/11/image_thumb10_thumb.png)