How to Receive an Email Alert when an Administrator account Logs in to Windows 10/11 or Windows Server.
Do you want to receive automatically an email alert every time an administrator logs into a Windows Server or in Windows 10/11 PRO? If so, continue reading below to learn how you can do this.
Sending automated email notifications when an admin account logs into Windows can enhance security by alerting administrators to potential unauthorized access. Monitoring admin logins can help you to detect unauthorized access attempts in real time and in this article, we’ll show you force a Windows computer to automatically send an email alert when an admin account logs in.
* Notes:
1. The instructions can be applied even on a Standard Windows Server or on a Domain controller.
2. The instructions can also be applied in Windows 11/10 Pro or Enterprise.
How to force Windows Server 2016/2019 or Windows 10/11 PRO to send an email notification when any administrator account is logged in.
-
Requirement: An SMTP server for sending emails.
Step 1. Create a PowerShell Script to send email notifications when administrators log in.
The first step to completing this task is to create a PowerShell script that will automatically send an email when an admin account logs on to the server. *
* Note: If you want to receive an email notification when any user logs on to the computer, use the script provided at the end of this article which also works for the Remote Desktop (RDP) users.
1. Create a folder named "Scripts" on your C:\ drive or any other folder where you want to store the PowerShell script that will send the email. *
* Note: In this guide we created the scripts folder in "C:\Windows\System32\Scripts".
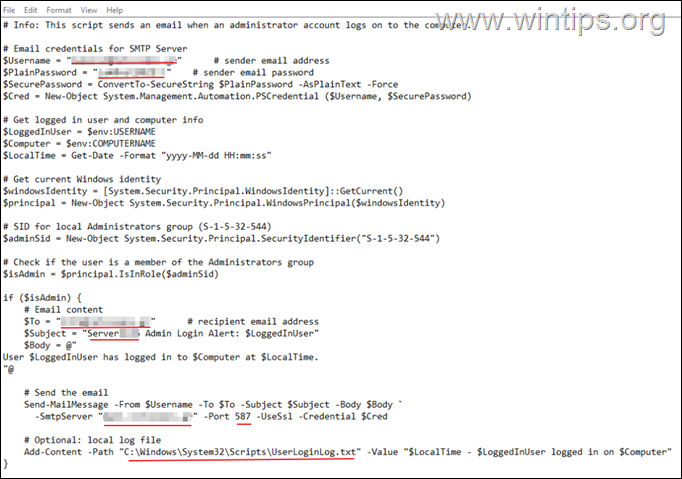
2. Now open Notepad and copy–paste the following text to create the script:
# Info: This script sends an email when an administrator account logs on to the computer.
# Email credentials for SMTP Server
$Username = "sender@domain.com" # sender email address
$PlainPassword = "senderpassword" # sender email password
$SecurePassword = ConvertTo-SecureString $PlainPassword -AsPlainText -Force
$Cred = New-Object System.Management.Automation.PSCredential ($Username, $SecurePassword)# Get logged in user and computer info
$LoggedInUser = $env:USERNAME
$Computer = $env:COMPUTERNAME
$LocalTime = Get-Date -Format "yyyy-MM-dd HH:mm:ss"# Get current Windows identity
$windowsIdentity = [System.Security.Principal.WindowsIdentity]::GetCurrent()
$principal = New-Object System.Security.Principal.WindowsPrincipal($windowsIdentity)# SID for local Administrators group (S-1-5-32-544)
$adminSid = New-Object System.Security.Principal.SecurityIdentifier("S-1-5-32-544")# Check if the user is a member of the Administrators group
$isAdmin = $principal.IsInRole($adminSid)if ($isAdmin) {
# Email content
$To = "recipient@domain.com" # recipient email address
$Subject = "SERVERNAME Login Alert: $LoggedInUser"
$Body = @"
User $LoggedInUser has logged in to $Computer at $LocalTime.
"@# Send the email
Send-MailMessage -From $Username -To $To -Subject $Subject -Body $Body `
-SmtpServer "mail.domain.com" -Port 587 -UseSsl -Credential $Cred# Optional: local log file
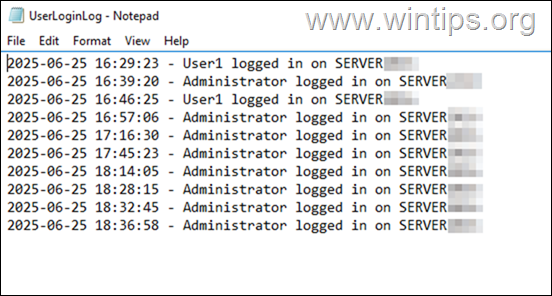
Add-Content -Path "C:\Windows\System32\Scripts\UserLoginLog.txt" -Value "$LocalTime – $LoggedInUser logged in on $Computer"
}
3. Then modify the script text as follows:
- Replace "sender@domain.com" with your sender email address.
- Replace "senderpassword" with your sender's email address password.
- Replace "recipient@domain.com" with the recipient’s email address.
- Replace "SERVERNAME" with the name of your Windows server.
- Replace "mail.domain.com" with the name of your SMTP server.
- Replace -if needed- "587" with your SMTPS server's port.
- Replace "C:\Windows\System32\Scripts" with the full path of the "Scripts" folder (if you created it on another location).
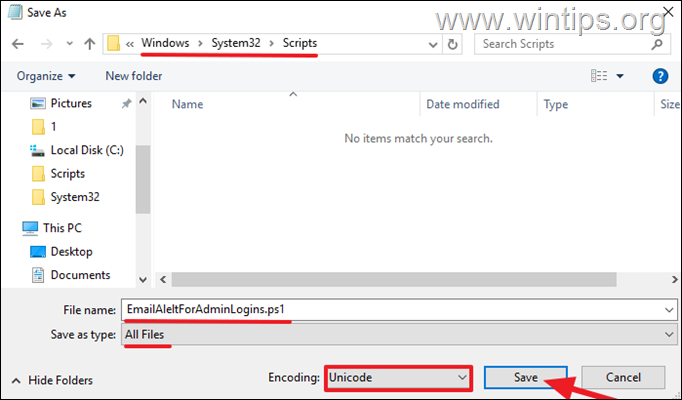
4a. When done, from File menu select Save As.
4b. Now do the following in "Save as" dialog:
- Select to save the file inside the "Scripts" folder you created before.
- Choose in Save as type: All Files
- Choose in Encoding: Unicode
- Type as File name: "EmailAleltForAdminLogins.ps1"
- Click Save and then close the Notepad.
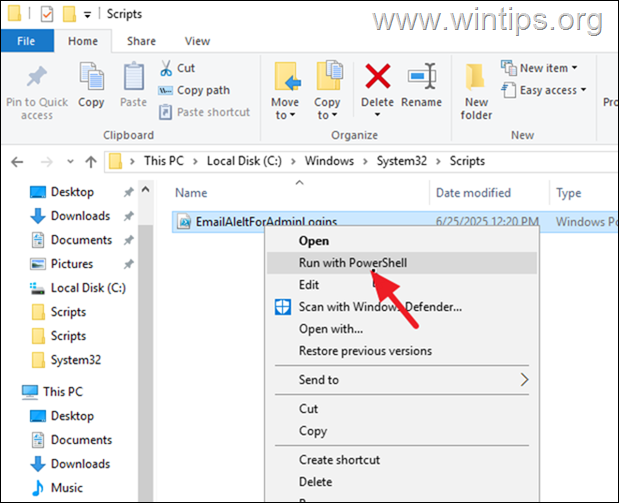
Step 2. Test the PowerShell script you created.
After you create the script, check if it works before proceeding further. To do this:
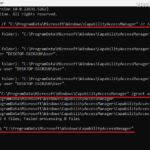
1. Right-click on the "EmailAleltForAdminLogins.ps1" and select Run with PowerShell.
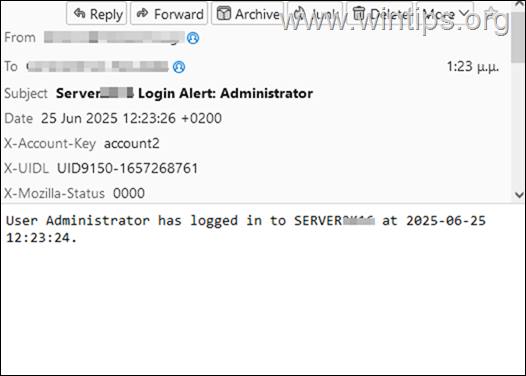
2. If the script works, then you should receive an email to the recipient address you entered in the script, notifying you that the "Administrator" account was logged into the server at the time you ran the script. If so, continue to next step.
Step 3. Force Windows to run the Script at Logon via Group Policy.
Now go ahead and configure Windows to run the script you created at "Logon" phase via local group policy.
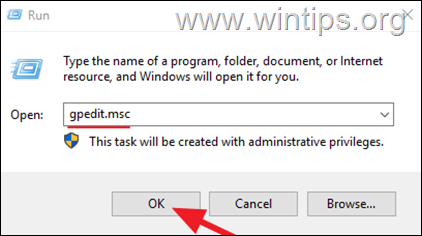
1. Simultaneously press the Windows ![]() + R keys to open the ‘Run‘ command box.
+ R keys to open the ‘Run‘ command box.
2. In Run command box, type gpedit.msc and press Enter (OK) to open the Local Group Policy Editor.
3. In Local Group Policy Editor navigate to the following location:
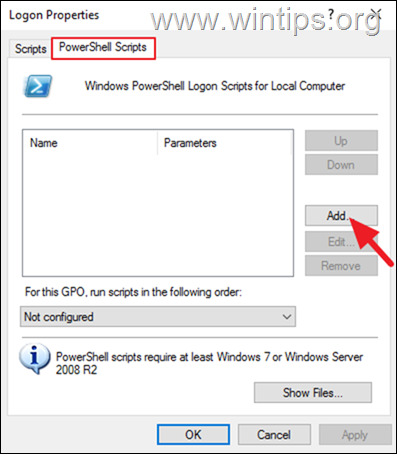
- User Configuration > Windows Settings > Scripts (Logon/Logoff) > Logon
4a. In 'Logon Properties' window select the PowerShell Scripts tab and click Add.
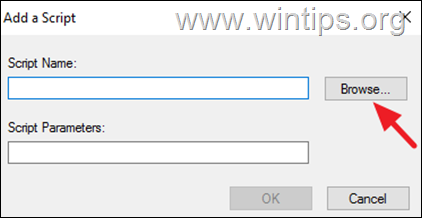
4b. On the 'Add a Script' window click Browse
4c. Navigate to the folder where you saved the script file you created (eg. the "C:\Windows\System32\Scripts\" folder in this example), select the "EmailAleltForAdminLogins.ps1" script file and click Open.
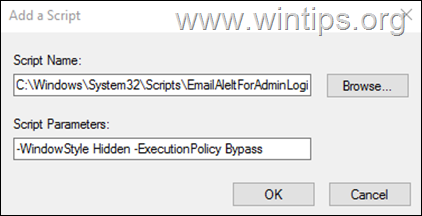
4d. Then, copy-paste the below text in Script Parameters field and click OK:
-
-WindowStyle Hidden -ExecutionPolicy Bypass
4e. Finally click Apply > OK and close the Local Group Policy Editor.
5. Now either restart the server to apply the policy or run "gpupdate /force" in command prompt and then Sign-Out from Windows.
6. Log back into the server and after a few seconds you will be notified via email about this login event. The login event will also be logged in the "UserLoginLog.txt" file located inside the "Scripts" folder (e.g. "C:\Windows\System32\Scripts\UserLoginLog.txt" in this example).*
* Notes:
1. Since the above script will only run at "Logon" (eg. thus means when you restart the server or if the admin account sign-out and logs back in to the server), and not when the server is unlocked, go ahead and force Windows to also send an email alert even when unlocking the server. To do this, read the instructions on step-2 of in this tutorial: How to Receive Email Notifications when a Windows Server or Windows 10/11 server is Unlocked.
2. The PowerShell script you created in step 1 sends an email notification only when the logged in user belongs to the Administrators group. If you want to be notified of any user connection to the machine, even for users connecting via Remote Desktop (RDP Connected Users), use the following script:
# Info: This script sends an email when any user account logs on to the computer.
# Email credentials for SMTP Server
$Username = "sender@domain.com" # sender email address
$PlainPassword = "senderpassword" # sender email password
$SecurePassword = ConvertTo-SecureString $PlainPassword -AsPlainText -Force
$Cred = New-Object System.Management.Automation.PSCredential ($Username, $SecurePassword)# Email content
$LoggedInUser = $env:USERNAME
$Computer = $env:COMPUTERNAME
$LocalTime = Get-Date -Format "yyyy-MM-dd HH:mm:ss"
$To = "recipient@domain.com" # recipient email address
$Subject = "ServerName Login Alert: $LoggedInUser"
$Body = @"
User $LoggedInUser has logged in to $Computer at $LocalTime.
"@# Send the email
Send-MailMessage -From $Username -To $To -Subject $Subject -Body $Body `
-SmtpServer "mail.domain.com" -Port 587 -UseSsl -Credential $Cred# Optional: local log file
Add-Content -Path "C:\Windows\System32\Scripts\UserLoginLog.txt" -Value "$LocalTime – $LoggedInUser logged in on $Computer"
That's it! Let me know if this guide has helped you by leaving your comment about your experience. Please like and share this guide to help others.
Frequently Asked Questions
What is the advantage of sending automated email notifications for admin logins?
Sending automated email notifications when an admin account logs into Windows can enhance security by alerting administrators to potential unauthorized access. This allows real-time detection of unauthorized access attempts.
Can these instructions be applied to standard Windows Servers and domain controllers?
Yes, the instructions can be applied to both a Standard Windows Server and a Domain Controller. They are also applicable for Windows 10/11 Pro or Enterprise.
What is the necessary requirement for sending email notifications when an admin logs in?
An SMTP server is required for sending email notifications when an administrator logs in.
How does the PowerShell script identify if the logged-in user is an administrator?
The script uses the SID for the local Administrators group (S-1-5-32-544) and checks if the logged-in user is a member of this group using Windows identity and principal objects.