How to Find Out Last Password Change in Active Directory Server 2016/2019.
If you want to find out the last password change for a user in Active Directory then continue reading this tutorial. This article contains instructions on how to view in Active Directory when a user last changed their password.
How to View the Last Password Change for a User in Active Directory 2019/2016/2012.
Method 1. Find Out the Last Change of User Password from Windows GUI.
If you need to find out the date of the last password change of a user in Active Directory:
1. Open Active Directory Users and Computers
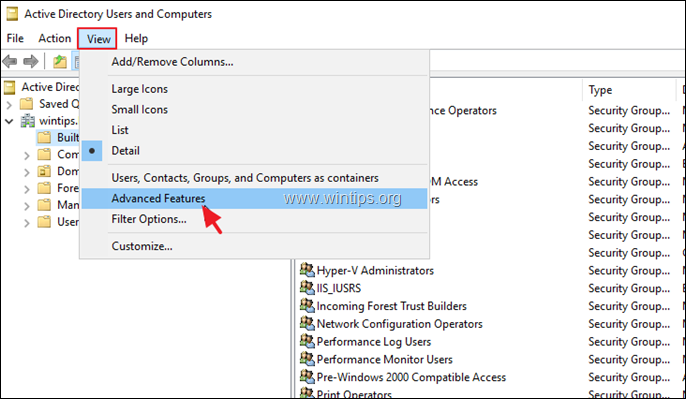
2. From View menu, click Advanced Features.
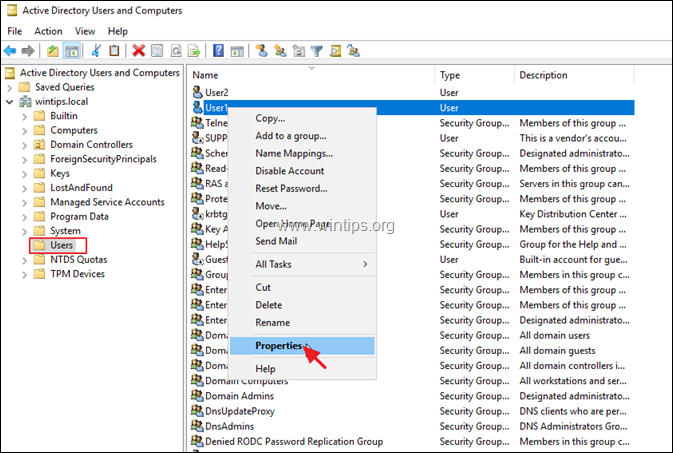
3. Select the Users group on the left pane.
4. At the right pane, right-click at the user you want to view the last password change and select Properties.
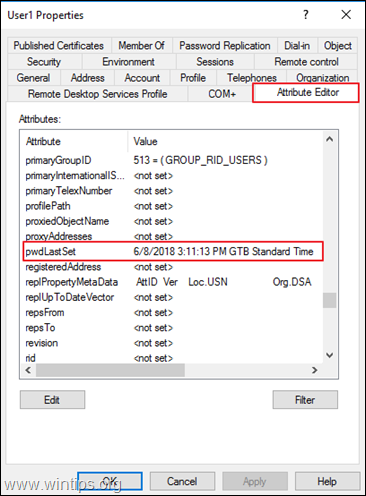
5. At 'User Properties' window, select the Attribute Editor tab.
6. Now scroll down to pwdLastSet attribute, to find out when a password was changed for last time.
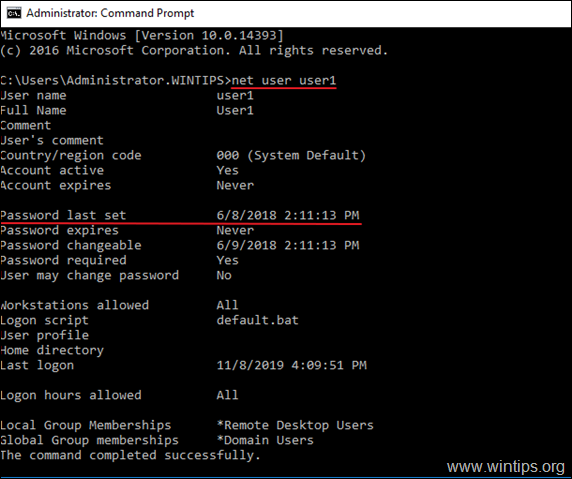
Method 2. Check the Latest User Password Change from Command Prompt.
The next method to see when a password was changed for a user, is to give the following command in Command Prompt or in PowerShell.
- net user AccountName
* Note: Where "AccountName" = the name of the domain user that you want to view the Password last set.
That's it! Let me know if this guide has helped you by leaving your comment about your experience. Please like and share this guide to help others.
- FIX: Device encryption is temporarily suspended and does not resume after the computer restarts (Windows 11). - May 5, 2026
- How to Install Chrome or any 'Line of Business' app on Intune Enrolled Windows Devices. - April 29, 2026
- How to Create a DDM Update Policy for iOS Devices in Intune. - April 23, 2026




February 17, 2022 @ 2:07 pm
works on 2012 as well.