How to Protect from Ransomware Attacks.
In the last years many ransomware variants have affected many home and business computers, in order to gain money for criminals. In the past few months, companies, schools, hospitals and many home users were the victims of ransomware attacks and they experienced the nightmare of losing their archives.
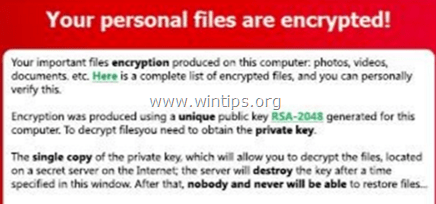
Ransomware is a type of malware that once it infects a computer, it encrypts with strong encryption all the data (word documents, excel files, pictures, etc.) that are stored on the local and all connected drives (external USB disks or/and the network drives/shares). After the encryption, the user-victim cannot open his files (because they have become locked or corrupted) and is informed by a screen alert that in order to remove the encryption, he must pay the demanded ransom, otherwise all his data will be lost.
The demanded ransom varies (e.g. $300, $500, $1000 or more) and must be paid in digital currency (e.g. BitCoins, PaySafe, etc.) by using the Tor Internet Browser, so it is impossible to catch the criminals.
How to prevent Ransomware attacks?
According to many security companies and organizations, 2016 is the year of Ransomware. Ransomware viruses can bypass all security tools (Antivirus, Firewall, etc.) because they are always updated with new versions by their "creators", in order to be undetectable. So, in a few words, if you want to prevent ransomware to destroy your work you have to:
1. Be Prepared by backing up your files to external storage devices and keep your backups offline, in order to reduce the data loss. (see Part-1 for instructions)
2. Be Careful with the emails and the attachments you receive. Think before visiting an HTML link or before opening attachments received by e-mail and never enable macros in documents received by e-mail, unless you have previously verified with the sender of the email that the document is legitimate . (see Part-2 for instructions)
3. Be protected by having your security software always updated, by installing an anti-ransomware tool and by specifying clear access rules to your computer and your files. (see Part-3 for instructions)
This Ransomware protection guide contains detailed instructions on how to protect your computer and your files from ransomware and malware infections.
How to Protect from Malware Attacks (Ransomware Protection Guide).
Part 1. BE PREPARED.
Step 1. Backup, backup and backup.
The most important and safest method to reduce the data disaster on your computer (or your network) from any type of damage (hardware or software) is to regularly perform backups of your files to another media (e.g. to an external USB Disk, cloud storage, etc.) and keep that media OFFLINE (NOT connected to the computer).
- Related articles:
1. How to Backup your Personal Files with SyncBackFree
2. How to Backup your Personal Files with Windows Backup.
Step 2. Enable System Protection on all disks.
The System Protection feature (in Windows 10, 8, 7 & Vista OS) gives you the opportunity to restore your system to a previous working state (System Restore) and to restore your files to a previous version, if needed (e.g. if your system doesn't boot normally after an update or after a virus attack). To accomplish these tasks, the System Protection, periodically takes snapshots of your current system state and files, that are named "Shadow Copies" *.
* Note: The latest versions of ransomware viruses delete the Shadow Copies from your system and disable the System Protection on your disks. But, if you 're lucky and notice directly the ransomware infection, (before Shadow Copies removal) then you 'll be able to restore your files to previous versions.
1. To enable System protection to all drives on your computer:
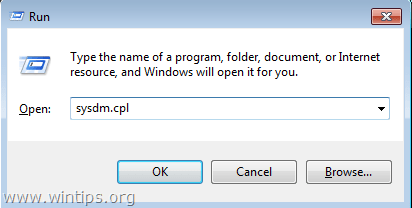
1. Press “Windows”
+ “R” keys to load the Run dialog box.
2. Type sysdm.cpl and press Enter.
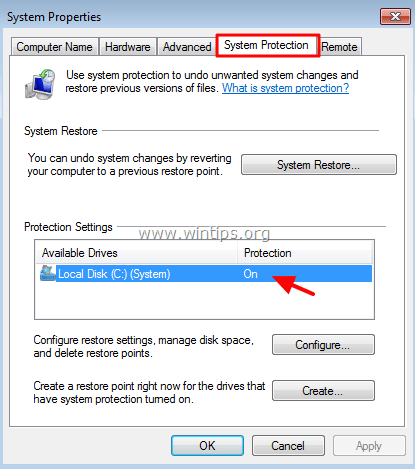
2. At System Protection tab, check if the Protection on your main drive is On.
4. If the Protection is Off or you want to view the protection settings or to enable the system protection to the rest drives, then:
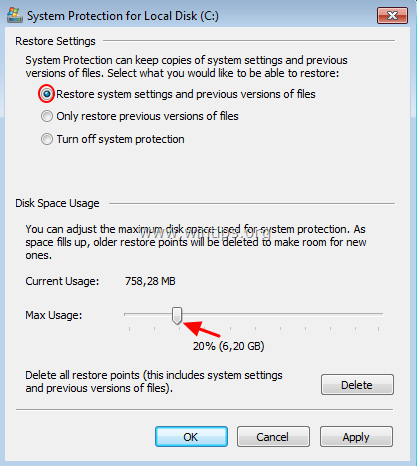
a. Choose the drive that you want to enable protection and click Configure.
b. Put the Max Usage slider at 15-20% (at least) and click OK.
Part 2. BE CAREFUL with Emails and Attachments!
The most common way that Ransomware viruses arrive is through an email that contains a malicious attachment or a malicious HTML link. These types of emails trick people to think that the email is coming from a trusted sender and encourage the user to open the attachment or the HTML link in order to find out the important information contained. So, think before opening any email and more specifically:
1. BE SUSPICIOUS when you receive an email with a document attachment* that is supposed to be an invoice, an offer, a bank notice or a bill, etc. that you don't expect.
* e.g. If the malicious attachment is named "Invoice_231244.doc" then it is probably fake and contains a virus.
2. DO NOT ENABLE MACROS in a document (word or excel) received by email or Internet that prompts or advises you* to enable macros in order to properly view its contents. If you Enable Macros, then you will run a code to encrypt you files.
* e.g. If you receive the following message while opening a document received by e-mail: "Enable Macros if the data is incorrect", don't enable Macros and delete the email immediately.
3. NEVER OPEN attachments from unsolicited emails with tricky text messages* which prompt you to open the included attachment, in order to see the important details that the document contains. Cyber criminals often send fake email messages that look legitimate and like as notifications from the bank, the tax collection system, an online store, etc.
* e.g. The email text message may say: "Dear Sir, Please see the attached invoice (MS Word document) and remit payment according the terms listed at the bottom of the invoice".
4. DO NOT VISIT HTML LINKS from unsolicited emails (or pop-up messages) that trick you to view or to download material from the Web.
5. DO NOT OPEN emails from unknown (or known) senders, with suspicious attachments (.doc, .zip, .exe, etc.) or suspicious HTML links.
6. Finally, open with caution emails from people you don't know and only if they appear to be legitimate.
Additional Practices to Prevent Ransomware & Malware Infections.
1. DO NOT VISIT malicious websites, like sites that automatically redirect you to other sites or continuously open pop-up windows.
2. DO NOT INSTALL or EXECUTE (run) programs that come from unknown sources. For example: Do not install programs that are supposed to clean or optimize your computer, or web browser plugins that are supposedly needed to view properly the contents of a website.
3. DO NOT OPEN an email titled "Your bank account has been frozen. Action required", because it is clearly an attempt to steal your bank credentials. (Banks don't send or require such information by email!).
4. DO NOT FILL OUT ONLINE FORMS with your personal information, until you check if the website is legal, with explained reasons about the usage of the information received, the contact details of the information collector, the proper design and official logos of the website creator and his purposes.
5. NEVER SHARE PERSONAL MATERIAL (e..g, photos, documents, etc.) or information (such as your full name, date of birth, telephone number, street address, credit card number) with unknown people or unknown sites.
Part 3. BE PROTECTED.
Step 1. Install an Anti-Ransomware Program.
Install one of the following Anti-Ransomware programs to prevent ransomware attacks:
- Malwarebytes Anti-Ransomware (Free): Malwarebytes Anti-Ransomware Beta is a program that protects your computer from file encrypting ransomware programs.
- Bitdefender Anti-Ransomware (Free): Bitdefender anti-malware researchers have released a new vaccine tool which can protect against known and possible future versions of the CTB-Locker, Locky and TeslaCrypt crypto ransomware families by exploiting flaws in their spreading methods.
- Emsisoft Anti-Malware (~20€): Emsisoft Anti-Malware is fueled by a dual engine malware scanner for twice the malware cleaning power, with no extra resource requirements. On top of that, Emsisoft Anti-Malware can even remove potentially unwanted programs (PUPs) that overload your computer with resource wasting bloat.
- Kasperksy FREE ANTI-RANSOMWARE TOOL FOR BUSINESS is a free complementary tool for small and mid-sized business based on two core technologies: Kaspersky Security Network and System Watcher, which identify ransomware behavior patterns and protect Windows-based endpoints. The software is compatible with the third-party protection solutions installed on PCs and can serve as second opinion software for the most advanced cryptomalware protection.
Step 2. Set Software Restrictions Policies.
Ransomware viruses use specific paths on your computer, in order to run malicious executables and infect your system. So, a very good precaution to avoid this from happening, is to prevent executables (.exe applications) from running from these locations: %LocalAppData%, %AppData%, %Temp%, C:\Windows.
1. %LocalAppData%
- Windows 10, 8, 7/Vista: C:\Users\<username>\AppData\Local
- Windows XP: C:\Documents and Settings\<username>\Local Settings
2. %AppData%
- Windows 10, 8, 7/Vista: C:\Users\<username>\AppData\Roaming
- Windows XP: C:\Documents and Settings\<username>\Application Data
3. %Temp%
- Windows 10, 8, 7/Vista: C:\Users\<username>\AppData\Local\Temp
- Windows XP: C:\Documents and Settings\<username>\Local Settings\Temp
4. C:\Windows
To block executables from running (at the above locations), first make sure that your computer is virus/malware free and then:
- Apply the Software Restrictions Policies automatically by using the CryptoPrevent* tool. (Windows all Editions).
OR
- Apply the Software Restrictions Policies manually. (Windows 7 Pro, Ultimate or Server 2008 Editions).
* CryptoPrevent tool from Foolish.IT, is an Anti-Virus/Security Software Supplement, originally designed to prevent infection from the CryptoLocker threat which emerged in late 2013. Since that time, CryptoPrevent has grown into a robust solution, providing protection against a wide range of ransomware and other malware.
Step 3. Set Clear Policies on your Computer or Network
1. Create a secondary account on your computer with limited privileges (Standard Account), especially if the same computer is used by more than one person (e.g. your child/children).
2. Specify unique and strong login credentials (Username and Password) for every user that has access to your computer or your network.
3. Secure the shared folders on your computer or network by specifying only the necessary rights (Read/Write/Modify/Delete) to every user that has access and do not give to users more power on the shared folders than they need.
Additional Steps To Protect Your Computer from Ransomware, Malware, etc.
1. APPLICATION WHITELISTING: The Application Whitelisting is a practice that grants access only to specific programs to run and deny the access to unknown programs. By using this Application Whitelisting the user specifies a list of applications that are allowed to run (whitelist) and forbids the execution of all other applications that are not included in the list. BleepingComputer has published an interesting article on How to create an Application Whitelist Policy in Windows.
2. ANTIVIRUS: Install an antivirus/security program on your system and keep it updated. Also periodically scan your system for viruses or malware infections.
- Related Articles:
3. WINDOWS UPDATE: Always keep Windows updated with the latest updates.
ONCE AGAIN: The most important action you must take in order to reduce the risk of loosing your files, is to periodically back-up your files to other media and keep that media OFFLINE.
That's it! Let me know if this guide has helped you by leaving your comment about your experience. Please like and share this guide to help others.