Remove Police Virus – FBI virus
(Updated on: 10/02/2013). The FBI Virus is a ransomware virus, that claims that your computer is locked because of law violations about “Copyright and Related Rights” or because you have accessed pornographic material. The FBI virus makes it impossible to work with your computer and asks you to pay a fee of 100$ or more to unlock it within 48 hours, otherwise your computer will be permanently locked and justice will take action against you.
The infection is caused through security vulnerabilities found when the user browses infected internet sites or downloads infected files. When your computer is infected by the FBI Virus, please don’t panic and follow the easy steps bellow to disinfect your system.

FBI Virus Removal Instructions.
How to disinfect your computer from the “FBI Virus”.
Method 1: Restore your computer to a previous working state.
(Watch this method on YouTube)
Notice: This method is usually effective only for the first version of FBI Police virus. If you cannot remove FBI Police virus using this method then follow steps in method No2 to remove this nasty virus.
Step 1. Stop FBI virus from running.
1. Shut down your computer by pressing the “Power” button continuously.
2. Start up your computer and as your computer is booting up, press the “F8” key before the Window logo appears.
3. For Windows 7: Using your keyboard arrows select the “Repair Your Computer” option and press “Enter”.
For Windows Vista or XP: Using your keyboard arrows select the “Safe mode” option and press “Enter”. In the next information message select “No” to start the “System Restore” application and continue to read here (7).

4. Choose your preferred input language in the first screen and press “Next”.
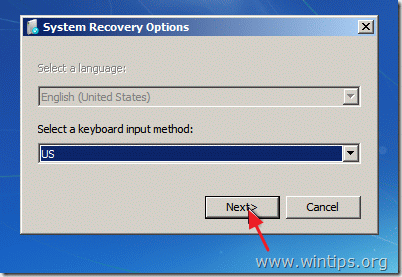
5. Input your login password and press “OK” to continue.

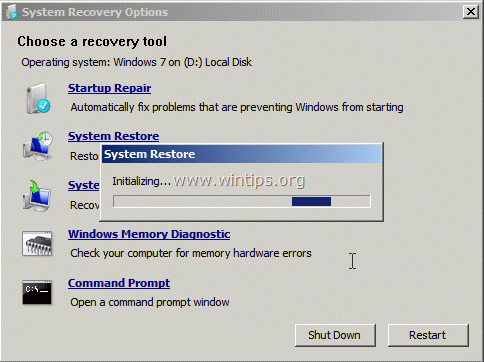
6. For Windows Vista or 7: Click on “System Restore” option.

7. At the next screen choose “Next”.
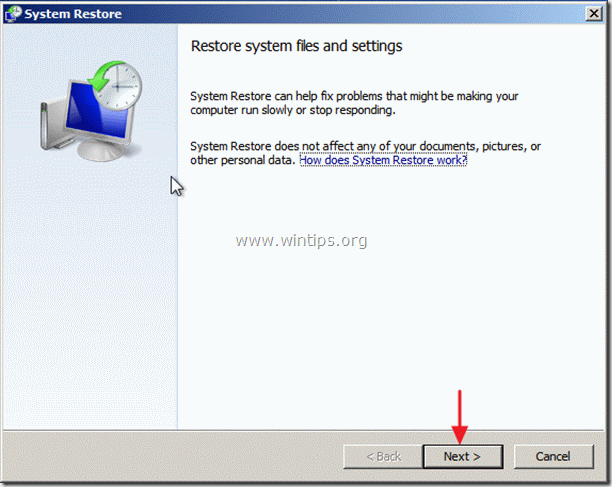
8. At the next screen choose a restore point date* before your computer was infected from “FBI Virus” and choose “Next”.
* If you don’t see all the restore points, check the “Show more restore points” option.

9. At the next screen, review your choices and press “Finish”

10. Wait until “System Restore” process is completed.
11. When the system restore is completed, restart your computer.

12. Continue to Step 2.
Method 2. Use RogueKiller to clean FBI Police Virus.
(Watch this method on YouTube)
1. From another computer download and save "RogueKiller" utility into a USB flash drive.
2. Start up your infected computer and, as your computer is booting up, press the “F8” key before the Windows logo appears.
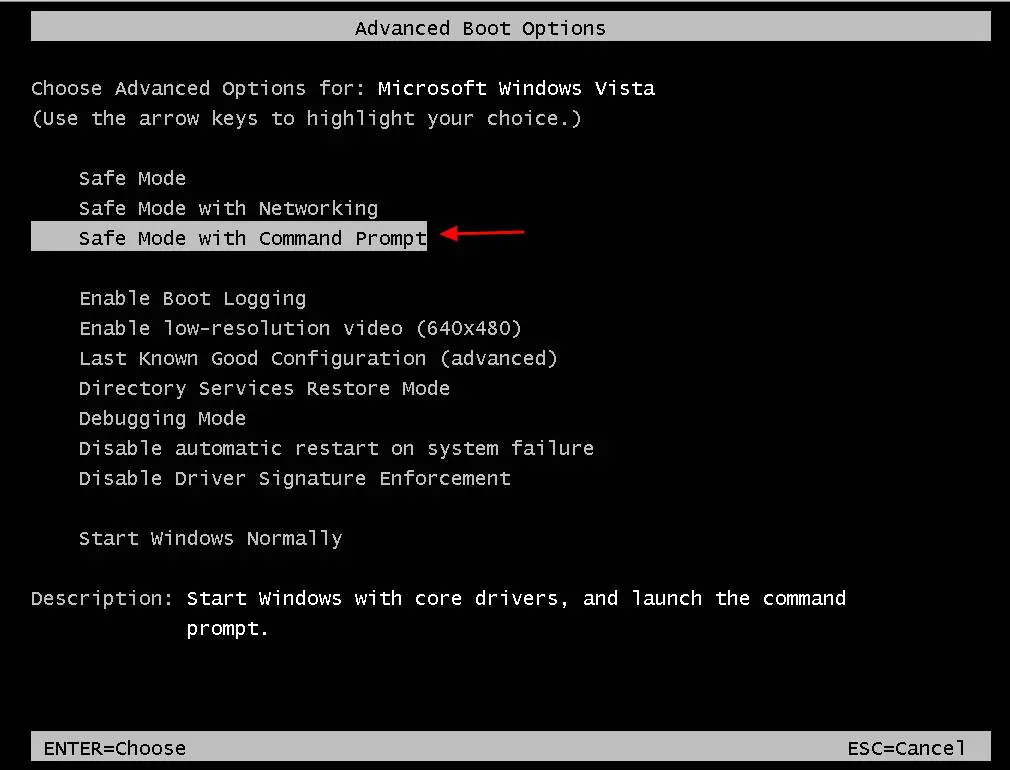
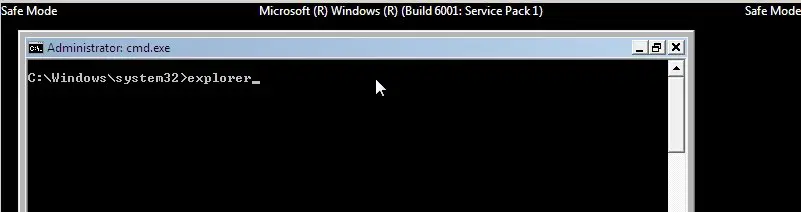
3. Using your keyboard arrows, select the “Safe Mode with command prompt” option and press “Enter”.
4. Inside command prompt window, type "explorer" and press "Enter".
5. Plug the USB drive into the affected computer and copy "RogueKiller" utility on your desktop.
6. Double Click to run RogueKiller. Let the prescan to complete and then press on "Scan" button to perform a full scan.
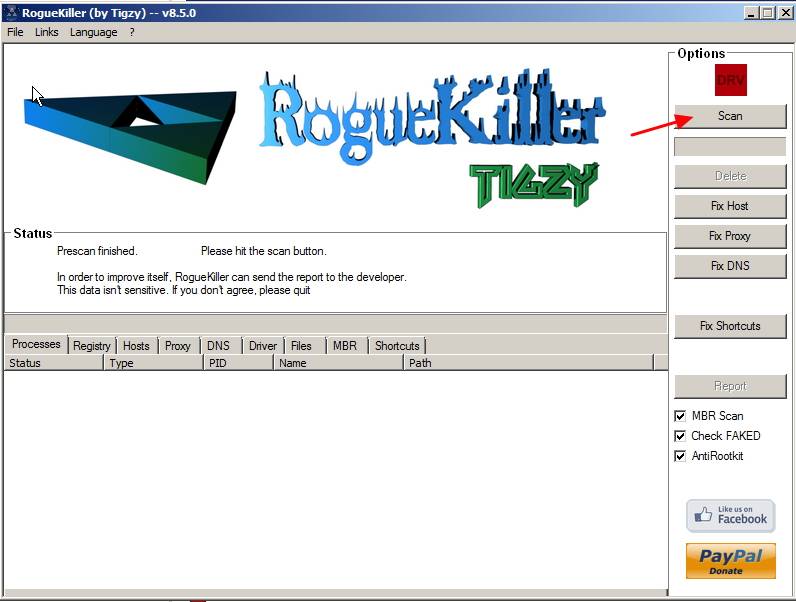
7. When full scan is completed, press the "Delete" button to remove all malicious items.
8. Restart your computer and continue to next step.
Step 2. Clean your computer from malicious threats.
Log on to windows and use “MalwareBytes Antimalware” program to clean your computer from malicious threats remaining on your computer.*
*If you don’t know how to install and use “MalwareBytes Anti-Malware“, read these instructions.
Advice: To ensure your computer is clean and safe, perform a Malwarebytes’ Anti-Malware full scan in windows “Safe mode“.*
*To get into Windows Safe mode, press the “F8” key as your computer is booting up, before the appearance of the Windows logo. When the “Windows Advanced Options Menu” appears on your screen, use your keyboard arrows keys to move to the Safe Mode option and then press “ENTER“.
Step 3. Clean unwanted files and entries.
Use “CCleaner” program and proceed to clean your system from temporary internet files and invalid registry entries.*
*If you don’t how to install and use “CCleaner”, read these instructions.
Step 4. Restart your computer for changes to take effect and perform a full scan with your antivirus program.
Notice*: This virus has a different name in every country. The removal procedure is almost always the same (the one described above), so you can try it if you have one of the versions bellow (please leave us a comment if it worked for you or not):
Please leave us a comment if it worked for you or not.
- "Australian Federal Police" virus (Australian version)
- "Computer is blocked"
- "CIBS POL" virus
- "Dirección General de la Policía" virus (Spanish version)
- "EC3 EUROPOL" virus
- “Firewall of the United States”
- "FBI Cybercrime Division" virus
- "Internet Crime Complaint Center" virus
- "ICE Cyber Crimes Center" virus
- "International Cyber Security Protection Alliance (ICSPA)" virus
- "Iός Αστυνομίας (Greek version)
- "LANDESPOLIZEIDIREKTION" virus (German version)
- "Ministrstvo za notranje zadeve" virus (Slovenija version)
- "New Zealand Police" virus (New Zealand version)
- "Police Central e-crime Unit" virus
- "Police Cybercrime Investigation Departament" virus
- "Policia Federal" virus (Argentina version)
- "Policia Boliviana" virus
- "Polizia Penitenziaria" virus (Italy version)
- "Poliisi Virus" (Finland version)
- "Politie Nederland Cybercriminaliteit" virus
- "POLÍCIA Departamento Cibercrime" virus (Portuguese version)
- "Polícia de Segurança Pública" virus (Portuguese version)
- "Police Grand-Ducale Luxembourg" virus
- "Policie České Republiky" virus (Česko version)
- "POLITI Kongeriget Danmark" virus (Danmark version)
- "Rikspolisstyrelsen Ukash" virus (Sweden version)
- "Royal Canadian Mounted Police (RCMP)" virus (Kanadian version)
- "Suomen Poliisi" (Suoen version)
- "Twój komputer został zablokowany" virus (Poland version)
- "Uw computer is geblokkeerd" virus (Nederland version)
- "United Kingdom Police" virus
- How to Add a Shared Calendar in Outlook for Web (OWA) - May 20, 2026
- How to Stop Windows 11 from Downgrading GPU Drivers. - May 18, 2026
- How to Update Third-Party Apps via Intune using WinGet AutoUpdate for Intune. - May 14, 2026



April 29, 2013 @ 2:25 am
It worked, Thanks!
April 3, 2013 @ 10:37 pm
AFTER STEP 3, REPAIR YOUR COMPUTER, MY COMPUTER GOES TO WHERE I NORMALLY ENTER MY PASSWORD. SHOULD I ENTER MY PASSWORD? IT DOESN'T SHOW SYSTEM RECOVERY OPTIONS BOX, CHOOSE YOUR LANGUAGE, LIKE STEP 4 SHOWS.
April 4, 2013 @ 7:36 am
Yes you should enter your password and then your system (normally) should display the System recovery options. (The language box is displayed only in systems with more than one languages specified to it).
March 20, 2013 @ 12:33 am
My problem is that the keyboard seems to be blocked, so I can't use the arrows to select safe mode. What should I do?
March 20, 2013 @ 10:12 am
Try to check the "NumLock" key status. If "Numlock" is "ON" you cannot use arrow keys. Press once your "Numlock" key and then try again.
If the problem persists please inform me what type of computer you have (Desktop or Laptop) and the Operating system installed on it.
Also in some laptops you must press "FN" (Function key) first while pressing arrows.
Good luck!
March 21, 2013 @ 11:56 am
Thanks a lot, but that's not the problem. It's a desktop, so there are arrows independent from the Numlock key. I read in some forums that this virus blocks all USB ports (obviously my keyboard is attached like that) and only the old keyboards work. I have no idea is this is true but started askind around if anyone has an old keyboard. Let me know if you have some better idea. I have Windows 7. thanks in advance!
March 21, 2013 @ 1:01 pm
Hello Bob. If you still not have found a PS2 Keyboard, then try this: Power off your computer by holding down (continuously) the power button when it loads Windows. Then turn on your computer and should be go to "Repair Options" (repair your computer). Then try to repair it using system restore options.
How to remove the Greek version of FBI virus money pack–“IOS ASTYNOMIAS”.
February 10, 2013 @ 12:11 pm
[…] For English visitors read here the English version of this article). O “Ιός της Ελληνικής […]