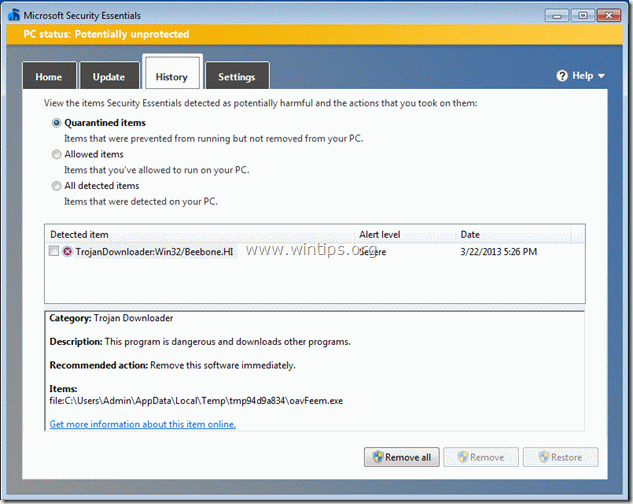
How to remove TrojanDownloader:Win32/Beebone.HI & Trojan ZbotR.Gen
"TrojanDownloader:Win32/Beebone.HI” virus is a dangerous Trojan downloader that can download and install malicious software on your computer. When the virus is installed, it drops malicious files into your computer, makes your system unstable and gives remote access to your computer. Win32/Beebone is a family of trojan downloaders that can access remote websites to download and run other malicious programs.
The malicious code can be installed when:
a. you click a malicious link posted on social networking sites.
b. when you open a file sent though an instant messaging program.
c. you open an email (PDF) attachment from unknown sender that claims that is from VISA card central.
Fake e-mail message sample:
{
Dear Visa card holder,
A recent review of your transaction history determined that your card was used in possible fraudulent transactions. For security reasons the requested transactions were refused. Please carefully review electronic report for your VISA card.
For more details please see the attached transaction report.
Lenore_Bass
Data Protection Officer
VISA EUROPE LIMITED
1 Sheldon Square
London W2 6WH
United Kingdom
CONFIDENTIALITY NOTICE: This electronic mail transmission and any attached files contain information intended for the exclusive use of the individual or entity to whom it is addressed and may contain information belonging to the sender (Visa Europe Limited.) that is proprietary, privileged, confidential and/or protected from disclosure under applicable law. If you are not the intended recipient, you are hereby notified that any viewing, copying, disclosure or distributions of this electronic message are violations of federal law. Please notify the sender, by email or telephone (+44 (0)20 7795 0273), of any unintended recipients and delete the original message without making any copies. Thank You
Attachment file: Recent_Activity.zip }
How to remove TrojanDownloader: Win32/Beebone.HI & Trojan ZbotR.Gen
Step 1: Terminate malicious process using RogueKiller
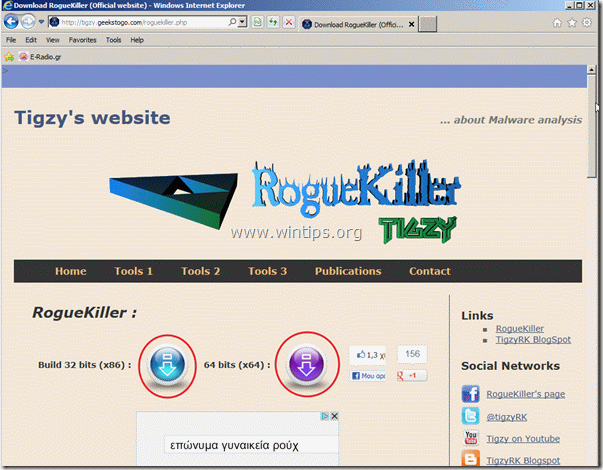
1. Download and save “RogueKiller” utility to your desktop.
Notice*: Download version x86 or X64 according to your operating system’s version*.
* To find your operating system’s version, “Right Click” on your computer icon, choose "Properties" and look at “System Type” section.
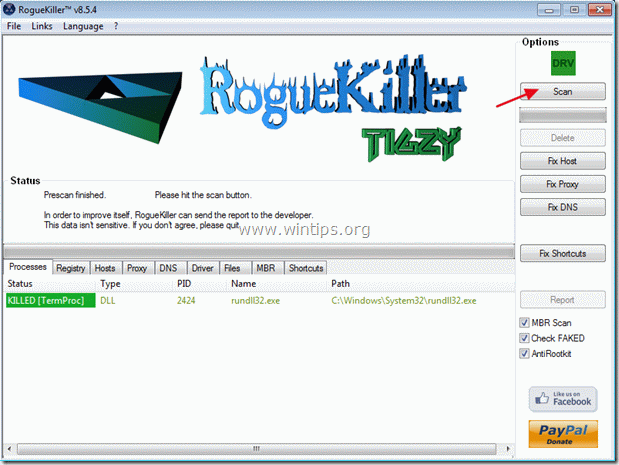
2. Find ”RogueKiller” on your desktop and double click to run it. Let prescan to complete (and terminate malicious process) and then press "Scan" button to perform a full scan.
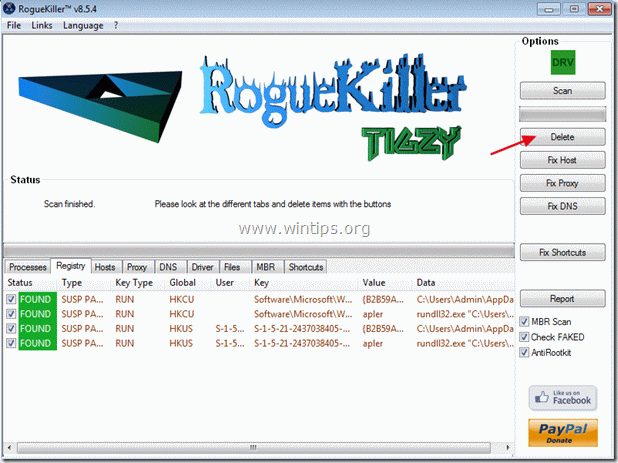
3. When full scan is completed, press “Delete” to remove all malicious items.
4. Close ”RogueKiller” and proceed to next step.
Step 2. Clean your computer from other malicious threats.
Download and install MalwareBytes Antimalware to clean all the malicious threats remaining on your computer.*
*If you don't know how to install and use "MalwareBytes Anti-Malware", read these instructions.
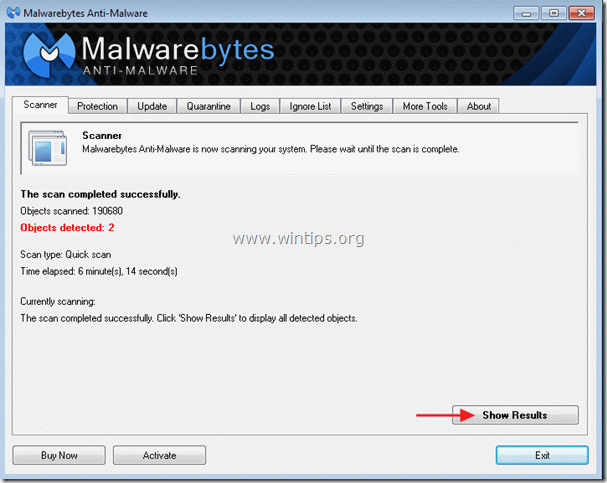
1. Run MalwareBytes Antimalware and perform a quick scan:
2. When the scanning is completed, press the "Show results" button to view and remove the malicious threats.
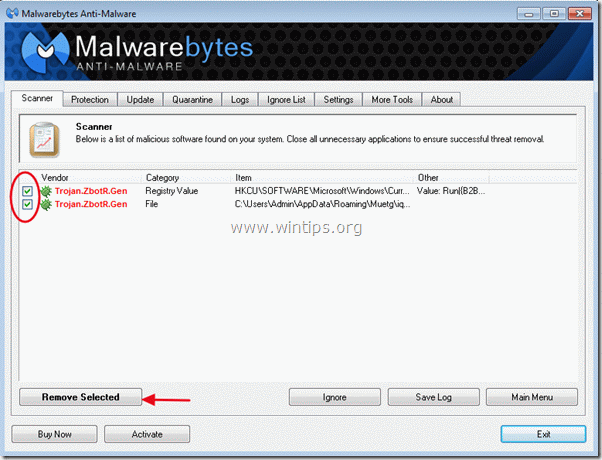
3c. At the "Show Results" window check – using your mouse's left button- all the infected objects and then choose the "Remove Selected" option and let the program remove the selected threats.
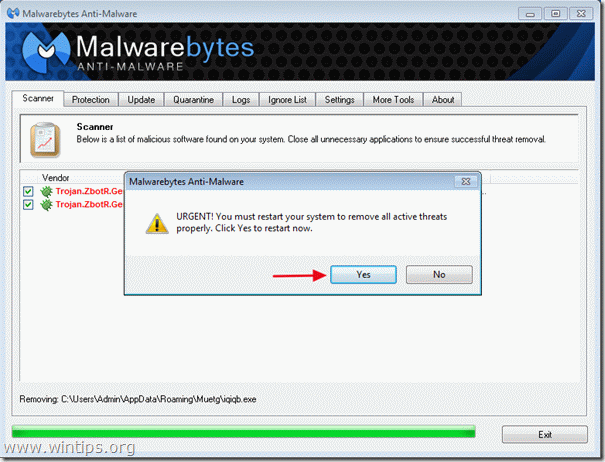
3d. When the removal of the infected objects process is complete, "Restart your system to remove all active threats properly.
4. Important: To ensure your computer is clean and safe, perform a full scan using Malwarebytes Anti-Malware, in Windows "Safe Mode".*
*To get into Windows Safe mode, press the "F8" key as your computer is booting up, before the appearance of the Windows logo. When the "Windows Advanced Options Menu" appears on your screen, use your keyboard arrows keys to move to the Safe Mode option and then press "ENTER".
Step 3. Clean unwanted files and entries.
Use "CCleaner" program and proceed to clean your system from temporary internet files and invalid registry entries.*
*If you don't how to install and use "CCleaner", read these instructions.
Step 4. Restart your computer for changes to take effect and perform a full scan with your antivirus program.
- FIX: Device encryption is temporarily suspended and does not resume after the computer restarts (Windows 11). - May 5, 2026
- How to Install Chrome or any 'Line of Business' app on Intune Enrolled Windows Devices. - April 29, 2026
- How to Create a DDM Update Policy for iOS Devices in Intune. - April 23, 2026