Remove “Trojan.FakePutt” from your system
“Trojan.FakePutt” is a malicious Trojan horse that gives access to your computer. When your computer is infected with this harmful program, it drops malicious files on your computer, makes your system unstable and gives remote access to your computer to unauthorized users.
The malicious “Trojan.FakePutt” code can be installed when:
a. you visit a malicious website
b. you install a fake update for your Internet browser.
c. you click a malicious link posted on social networking sites.
To remove “Trojan.FakePutt” malicious program and registry entries from your computer, follow the steps bellow:
How to remove Trojan “Trojan.FakePutt” from your computer:
Step 1: Clean you computer with RogueKiller
1. Download and save "RogueKiller" utility on your computer* (e.g. your Desktop).
Notice*: Download version x86 or X64 according to your operating system's version. To find your operating system's version, "Right Click" on your computer icon, choose "Properties" and look at "System Type" section
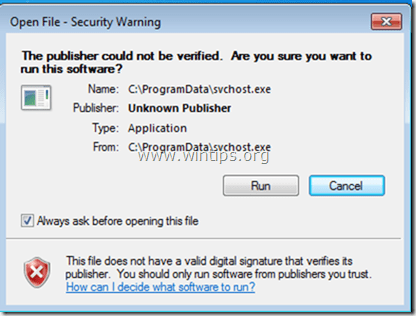
2. Double Click to run RogueKiller.
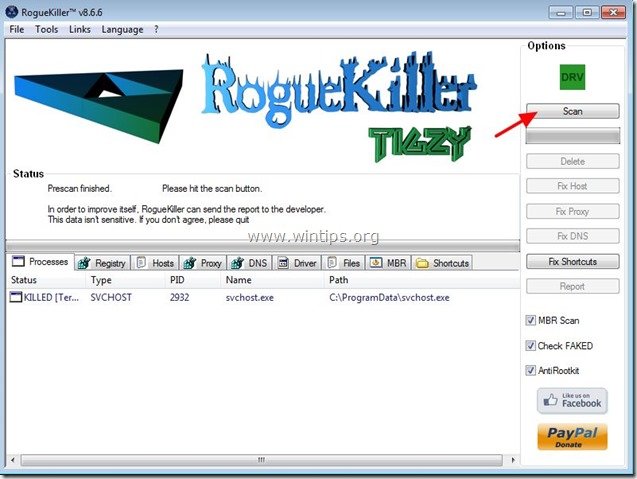
3. Let the prescan to complete and then press on "Scan" button to perform a full scan.
3. When the full scan is completed, press the "Delete" button to remove all malicious items found.
4. After RogueKiller removal process, continue to next step.
Step 2. Clean your computer from remaining malicious threats.
Download and install one of the most reliable FREE anti malware programs today to clean your computer from remaining malicious threats. If you want to stay constantly protected from malware threats, existing and future ones, we recommend that you install Malwarebytes Anti-Malware PRO:
Malwarebytes™ Protection
Removes Spyware, Adware & Malware.
Start Your Free Download Now!
1. Run "Malwarebytes Anti-Malware" and allow the program to update to it's latest version and malicious database if needed.
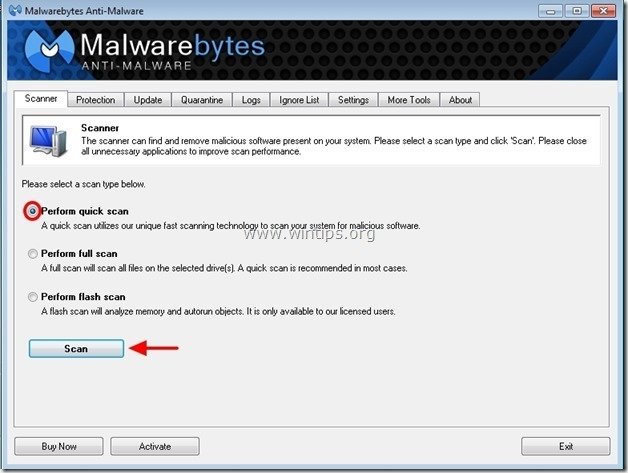
2. When the "Malwarebytes Anti-Malware" main window appears on your screen, choose the "Perform quick scan" option and then press "Scan" button and let the program scan your system for threats.
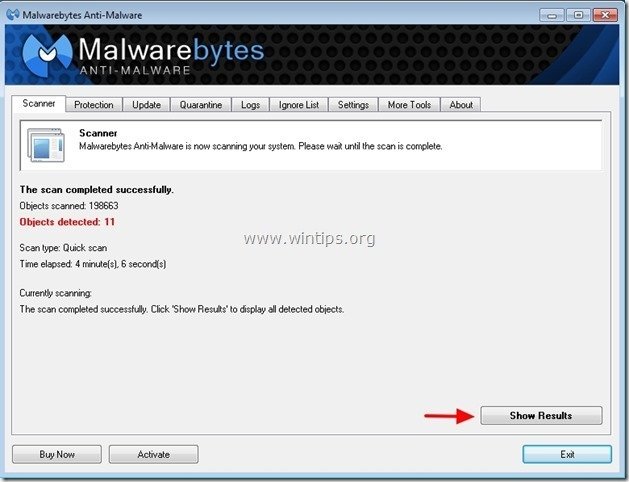
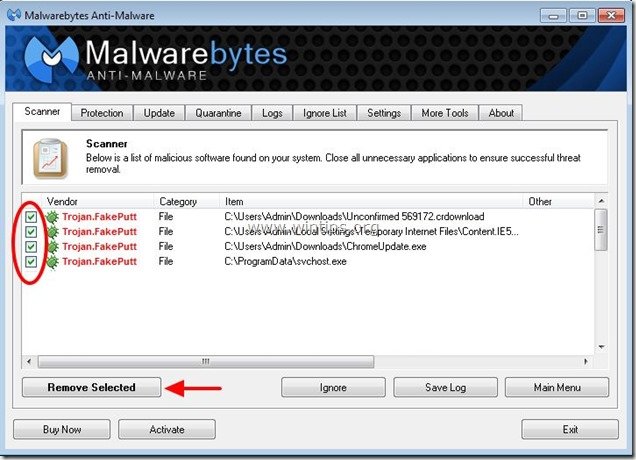
3. When the scanning is completed, press “OK” to close the information message and then press the "Show results" button to view and remove the malicious threats found.
4. At the "Show Results" window check – using your mouse's left button- all the infected objects and then choose the "Remove Selected" option and let the program remove the selected threats.
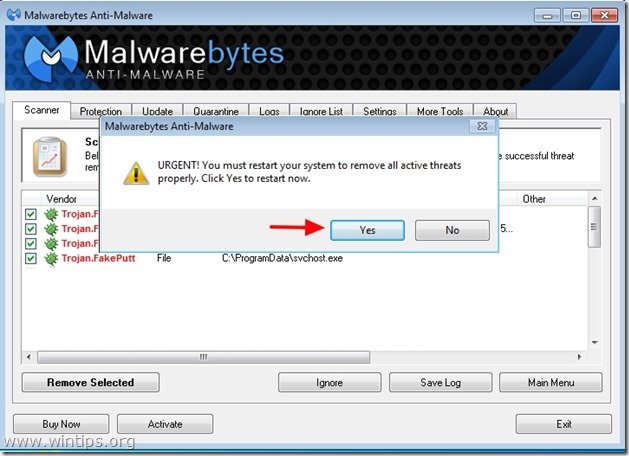
5. When the removal of infected objects process is complete, "Restart your system to remove all active threats properly"
6. Continue to the next step.
Advice: To ensure your computer is clean and safe, perform a Malwarebytes’ Anti-Malware full scan in windows “Safe mode“.*
*To get into Windows Safe mode, press the “F8” key as your computer is booting up, before the appearance of the Windows logo. When the “Windows Advanced Options Menu” appears on your screen, use your keyboard arrows keys to move to the Safe Mode option and then press “ENTER“.
Step 3. Clean unwanted files and entries.
Use “CCleaner” program and proceed to clean your system from temporary internet files and invalid registry entries.*
*If you don’t know how to install and use “CCleaner”, read these instructions.