How to Fix No Internet Access problem caused by Trojan.Delf Virus
When your computer suddenly doesn't connect to the Internet anymore, then probably you are infected with “Trojan.Delf” virus. The “Trojan.DELF” (also known as "Trojan:Win32/Delf.LN", "Trojan.Win32.Delf") is a malware program that spreads itself by sending malicious links to users through e-mail or instant messaging programs (e.g. Yahoo Messenger) and once it infects the target computer, it disables antivirus protection, blocks the Internet traffic (but you are connected) and downloads (and execute) malicious applications to the infected computer.
This tutorial is written to help users to get rid of "Trojan.Delf"virus and restore their Internet connection.
How to remove Trojan.Delf Virus.
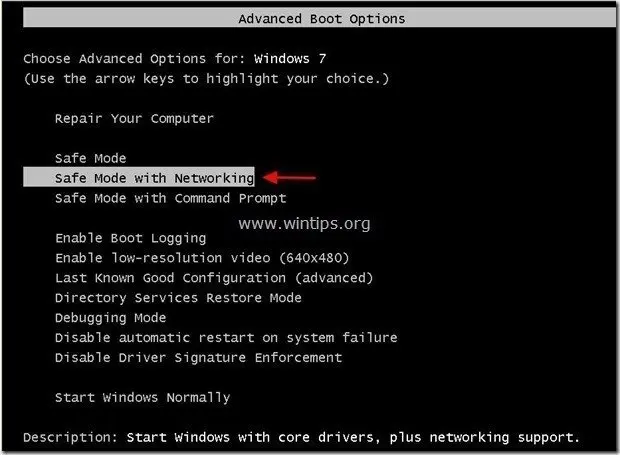
Step 1. Start your computer in Safe Mode With Networking
1. To get into Windows Safe mode, press the “F8” key as your computer is booting up (before the appearance of the Windows logo).
2. When the “Windows Advanced Options Menu” appears on your screen, use your keyboard arrows keys to move to the “Safe Mode with Networking” option and then press “ENTER“.
Step 2. Clean your computer from remaining malicious threats.
Download and install one of the most reliable FREE anti malware programs today to clean your computer from remaining malicious threats. If you want to stay constantly protected from malware threats, existing and future ones, we recommend that you install Malwarebytes Anti-Malware PRO:
Malwarebytes™ Protection
Removes Spyware, Adware & Malware.
Start Your Free Download Now!
Attention: If you cannot download MalwareBytes Antimalware on the infected computer, then you can download it on another clean computer and then transfer it (e.g. by using a USB flash disk) on the infected computer.
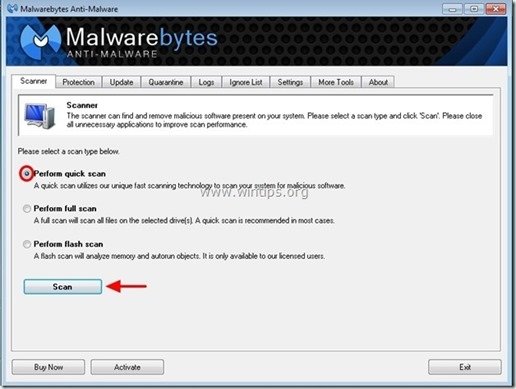
1. Run "Malwarebytes Anti-Malware" and allow the program to update to it's latest version and malicious database if needed.
2. When the "Malwarebytes Anti-Malware" main window appears on your screen, choose the "Perform quick scan" option and then press "Scan" button and let the program scan your system for threats.
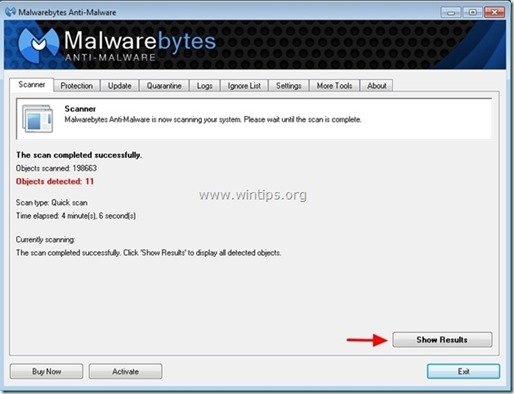
3. When the scanning is completed, press “OK” to close the information message and then press the "Show results" button to view and remove the malicious threats found.
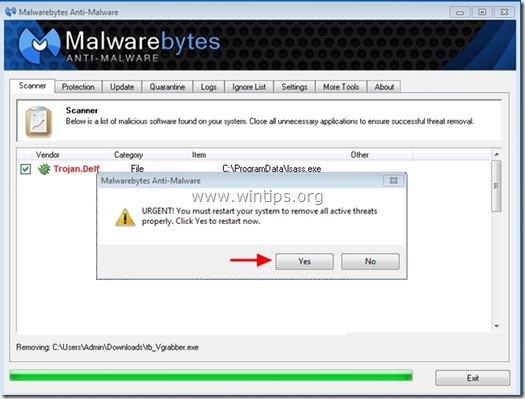
4. At the "Show Results" window check – using your mouse's left button- all the infected objects and then choose the "Remove Selected" option and let the program remove the selected threats.
5. When the removal of infected objects process is complete, "Restart your system to remove all active threats properly"
6. Continue to the next step.
Step 3. Clean unwanted files and entries.
Use “CCleaner” program and proceed to clean your system from temporary internet files and invalid registry entries.*
*If you don’t know how to install and use “CCleaner”, read these instructions.
Step 4. Perform a full scan with your antivirus program.
- How to Securely Allow SMTP Sending through Microsoft 365 using SMTP RELAY. - May 26, 2026
- How to Add a Shared Calendar in Outlook for Web (OWA) - May 20, 2026
- How to Stop Windows 11 from Downgrading GPU Drivers. - May 18, 2026




July 22, 2022 @ 2:58 pm
If you do this will it wipe all the contents/ files from the computer or will that stuff still be there after clearing the virus ?
July 24, 2022 @ 9:33 am
Your files will be there, but follow the steps in this guide which is updated.
October 20, 2016 @ 6:23 am
I cannot connect to the internet in safe mode with networking and I have malwarebytes installed and the virus stops it from scanning.
October 20, 2016 @ 8:58 am
Follow the steps in this guide to clean your system. (If you cannot download the mentioned tools from the infected computer, then download the tools from another clean computer and transfer them to the infected by using a USB stick)