How to remove Win32.Pmax.Gen Trojan Horse
Trojan Win32.Pmax.Gen is a dangerous malicious Rootkit that hides its existence from detection (and removal) and once it infects a computer, it can steal personal information, it redirects browsing results into advertisements from unknown publishers in order to earn money and it displays fake security alerts about problems that affect your computer's security.
Commonly, Win32.Pmax.Gen Trojan is bundled inside fake antivirus programs (Ransomware) that demand from the computer user to buy them, in order to fix all security issues found during their FAKE scan.
If a computer is infected with Win32.Pmax.Gen Trojan, then the antivirus security is disabled on it, the computer speed is decreased dramatically and continuously more ads are displayed on the computer screen.
Win32.Pmax.Gen Trojan can infect your computer if you visit a malicious website or if you download a FREE program from an unknown source or vendor.
To clean Win32.Pmax.Gen Trojan from your computer follow the steps bellow:
How to remove Trojan Win32.Pmax.Gen from your computer:
Step 1: Start your computer in “Safe Mode with Networking”
To do this:
1. Shut down your computer.
2. Start up your computer (Power On) and as your computer is booting up, press the "F8" key before the Windows logo appears.
3. Using your keyboard arrows select the "Safe Mode with Networking" option and press "Enter".
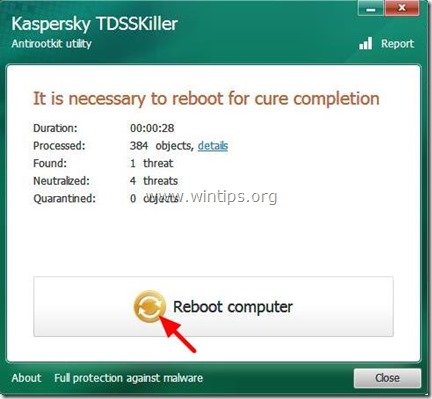
Step 2: Remove malicious Pmax.Gen Rootkit.
1. Download TDSSKiller Anti-rootkit utility from Kaspersky's website on your desktop.
2. When the download process is complete, go to your desktop and double click on “tdsskiller.exe” to run it.
3. At Kaspersky’s Anti-rootkit utility program click on “Start scan" to start scanning for malicious programs.
When the scan process is complete, a new window opens with the scanning results.
6. Choose "Delete" and press “Continue” to remove all threats found.
7. When the removal operation is complete, reboot your computer.
8. Start your computer in “Safe Mode with Networking” again.
9. After rebooting, run TDSSKiller again to scan one more time for Rootkits. If the previous curing job was completed successfully, the program now will inform you that "No Threats found".
Step 3: Clean you computer with RogueKiller
1. Download and save "RogueKiller" utility on your computer'* (e.g. your Desktop)
Notice*: Download version x86 or X64 according to your operating system's version. To find your operating system's version, "Right Click" on your computer icon, choose "Properties" and look at "System Type" section
2. Double Click to run RogueKiller.
3. Let the prescan to complete and then press on "Scan" button to perform a full scan.
3. When the full scan is completed, press the "Delete" button to remove all malicious items found.
4. Close RogueKiller utility and reboot your computer.
5. Start your computer in “Safe Mode with Networking” again.
6. Run RogueKiller again to ensure that ZeroAccess infection is completely removed.
7. Continue to the next step.
Step 4: Clean Adware and Malicious Registry entries using “AdwCleaner”
1. Download and save “AdwCleaner” utility to your desktop.
2. Close all open programs and Double Click to open ”AdwCleaner” from your desktop.
3. Press “Scan”.
4. When scan is completed, press “Clean” to remove all the unwanted malicious entries.
4. Press “OK” at “AdwCleaner – Information” and press “OK” again to restart your computer.
5. When your computer restarts, close "AdwCleaner" information (readme) window and continue to the next step.
Step 5. Clean your computer from remaining malicious threats.
Download and install one of the most reliable FREE anti malware programs today to clean your computer from remaining malicious threats. If you want to stay constantly protected from malware threats, existing and future ones, we recommend that you install Malwarebytes Anti-Malware PRO:
Malwarebytes™ Protection
Removes Spyware, Adware & Malware.
Start Your Free Download Now!
1. Run "Malwarebytes Anti-Malware" and allow the program to update to it's latest version and malicious database if needed.
2. When the "Malwarebytes Anti-Malware" main window appears on your screen, choose the "Perform quick scan" option and then press "Scan" button and let the program scan your system for threats.
3. When the scanning is completed, press “OK” to close the information message and then press the "Show results" button to view and remove the malicious threats found.
4. At the "Show Results" window check all items found (Right-Click > “Select All Items”) and then click on the "Remove Selected" button to remove all threats.
5. When the removal of infected objects process is complete, "Restart your system to remove all active threats properly"
6. Continue to the next step.
Advice: To ensure your computer is clean and safe, perform a Malwarebytes’ Anti-Malware full scan in windows “Safe mode“.*
*To get into Windows Safe mode, press the “F8” key as your computer is booting up, before the appearance of the Windows logo. When the “Windows Advanced Options Menu” appears on your screen, use your keyboard arrows keys to move to the Safe Mode option and then press “ENTER“.
Step 6. Clean unwanted files and entries.
Use “CCleaner” program and proceed to clean your system from temporary internet files and invalid registry entries.*
*If you don’t know how to install and use “CCleaner”, read these instructions.
Step 7. Restart your computer for changes to take effect and perform a full scan with your antivirus program.
- How to Add a Shared Calendar in Outlook for Web (OWA) - May 20, 2026
- How to Stop Windows 11 from Downgrading GPU Drivers. - May 18, 2026
- How to Update Third-Party Apps via Intune using WinGet AutoUpdate for Intune. - May 14, 2026


![safe-mode-with-networking_thumb1_thu[2]_thumb[1] safe-mode-with-networking_thumb1_thu[2]_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/safe-mode-with-networking_thumb1_thu2_thumb1_thumb.jpg)
![image_thumb29_thumb_thumb_thumb_thumb[1] image_thumb29_thumb_thumb_thumb_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/image_thumb29_thumb_thumb_thumb_thumb1_thumb.png)
![image_thumb26_thumb_thumb_thumb_thumb[1] image_thumb26_thumb_thumb_thumb_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/image_thumb26_thumb_thumb_thumb_thumb1_thumb.png)
![image_thumb17_thumb_thumb_thumb_thumb[1] image_thumb17_thumb_thumb_thumb_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/image_thumb17_thumb_thumb_thumb_thumb1_thumb.png)

![tdsskiller-start-scan122[2] tdsskiller-start-scan122[2]](https://www.wintips.org/wp-content/uploads/2014/01/tdsskiller-start-scan1222.jpg)

![tdsskiller-no-threats-found122[2] tdsskiller-no-threats-found122[2]](https://www.wintips.org/wp-content/uploads/2014/01/tdsskiller-no-threats-found1222.jpg)
![saa_thumb2_thumb_thumb_thumb_thumb_t_thumb[1] saa_thumb2_thumb_thumb_thumb_thumb_t_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/saa_thumb2_thumb_thumb_thumb_thumb_t_thumb1_thumb.jpg)
![roguekiller-scan_thumb1_thumb_thumb[1] roguekiller-scan_thumb1_thumb_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/roguekiller-scan_thumb1_thumb_thumb1_thumb.jpg)
![remove-zeroaccess-sireref-roguekiller_thumb[1] remove-zeroaccess-sireref-roguekiller_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/remove-zeroaccess-sireref-roguekiller_thumb1_thumb.jpg)
![remove-sireref-zeroaccess_thumb[1] remove-sireref-zeroaccess_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/remove-sireref-zeroaccess_thumb1_thumb.jpg)
![download-adwcleaner-home_thumb1_thum[1]_thumb[2] download-adwcleaner-home_thumb1_thum[1]_thumb[2]](https://www.wintips.org/wp-content/uploads/2014/01/download-adwcleaner-home_thumb1_thum1_thumb2_thumb.jpg)
![adwcleaner-scan_thumb1_thumb_thumb_t[1]_thumb[2] adwcleaner-scan_thumb1_thumb_thumb_t[1]_thumb[2]](https://www.wintips.org/wp-content/uploads/2014/01/adwcleaner-scan_thumb1_thumb_thumb_t1_thumb2_thumb.jpg)
![adwcleaner-clean_thumb1_thumb_thumb_[1]_thumb[4] adwcleaner-clean_thumb1_thumb_thumb_[1]_thumb[4]](https://www.wintips.org/wp-content/uploads/2014/01/adwcleaner-clean_thumb1_thumb_thumb_1_thumb4_thumb.jpg)

![ahefjplu_thumb2_thumb_thumb_thumb_thumb[1] ahefjplu_thumb2_thumb_thumb_thumb_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/ahefjplu_thumb2_thumb_thumb_thumb_thumb1_thumb.jpg)
![juygdz2u_thumb2_thumb_thumb_thumb_thumb[2] juygdz2u_thumb2_thumb_thumb_thumb_thumb[2]](https://www.wintips.org/wp-content/uploads/2014/01/juygdz2u_thumb2_thumb_thumb_thumb_thumb2_thumb.jpg)

![2by1vxhf_thumb1_thumb[1] 2by1vxhf_thumb1_thumb[1]](https://www.wintips.org/wp-content/uploads/2014/01/2by1vxhf_thumb1_thumb1_thumb.jpg)