How to remove Malware Protection rogue software
“Malware Protection” is a fake anti-spyware software and upon installed on your computer, it claims that malicious threats are found on your computer and you must buy the full version of the program to clean them.
The software gets in your computer when you download and install free software from unknown internet websites. Please ignore all fake warning messages and DO NOT give any money to purchase the full version.
To uninstall Malware Protection from your computer, proceed with the steps bellow:
How to remove Malware Protection from your computer.
Step 1: Start your computer in “Safe Mode with Networking”
To do this,
1. Shut down your computer.
2. Start up your computer (Power On) and as your computer is booting up, press the "F8" key before the Windows logo appears.
3. Using your keyboard arrows select the "Safe Mode with Networking" option and press "Enter".
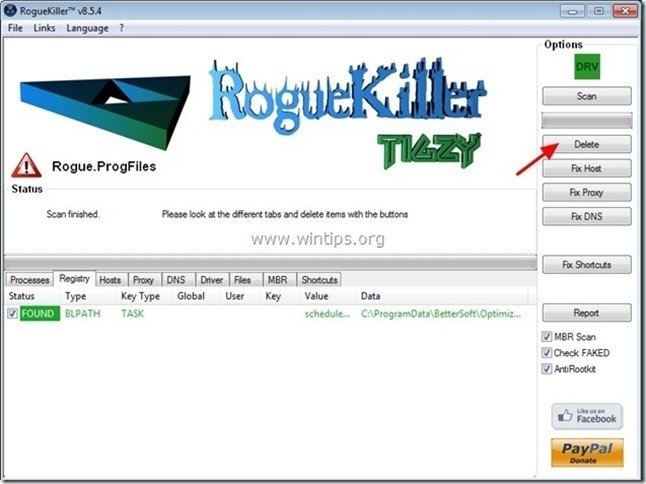
Step 2. Clean you computer with RogueKiller
1. Download and save "RogueKiller" utility on your computer'* (e.g. your Desktop)
Notice*: Download version x86 or X64 according to your operating system's version. To find your operating system's version, "Right Click" on your computer icon, choose "Properties" and look at "System Type" section
2. Double Click to run RogueKiller.
3. Let the prescan to complete and then press on "Scan" button to perform a full scan.
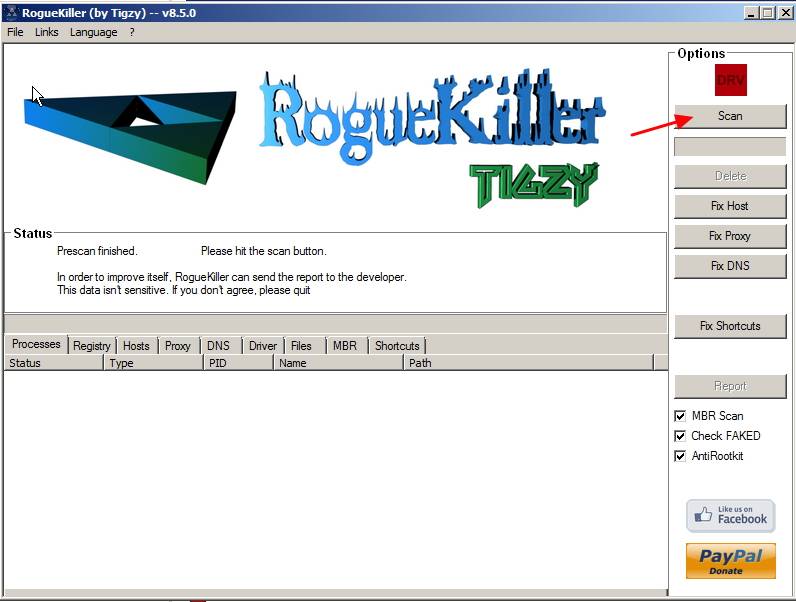
3. When the full scan is completed, press the "Delete" button to remove all malicious items found.
Step 3. Prevent malicious programs from running at Windows Startup.
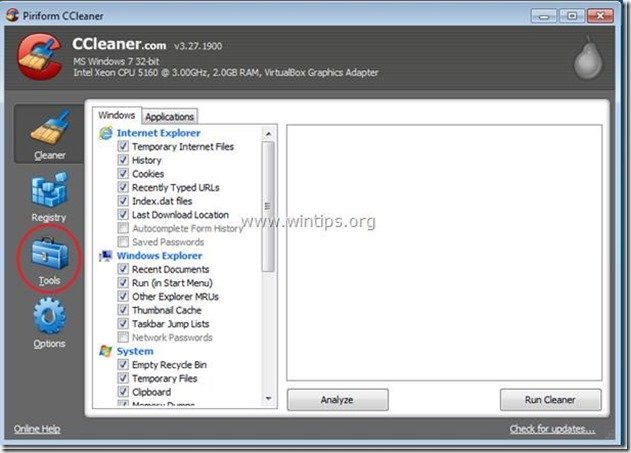
1. Download and run CCleaner.
2. At “CCleaner” main window, choose "Tools" on the left pane.
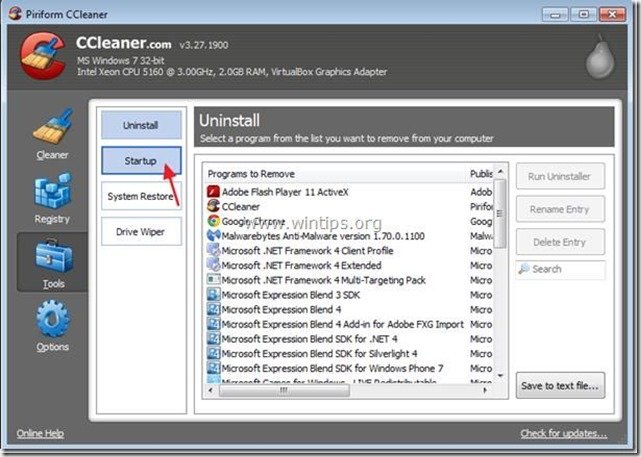
4a. In "Tools" section, choose "Startup".
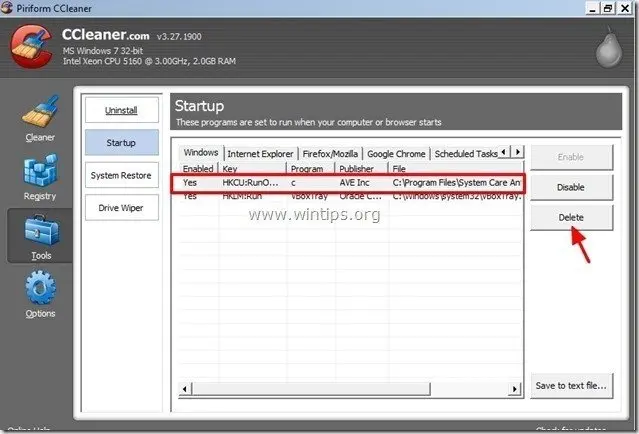
4b. Choose "Windows” tab and then select and delete all malicious programs running on Windows startup: *
- e.g. %AppData%\defender.exe
Additional Information*: Commonly this Rogue Antivirus runs from the following locations on your computer:
– “C:\ProgramData” (in Windows Vista, 7 or 8)
– “C:\Documents and Settings\<YourUserName>\Application Data” (Windows8,7, Vista)
– “C:\Documents and Settings\<YourUserName>\Application Data” ( Windows XP)
– “C:\Documents and Settings\All Users\Application Data” ( Windows XP)
“ C:\Program Files”
Malicious startup entries (example):
"Yes | HKCU:RunOnce | c | C:\ProgramData\RandomFileName.exe"
"Yes | HKCU:RunOnce | c | C:\ProgramData\RandomFolderName\RandomFileName.exe"
"Yes | HKCU:RunOnce | c | C:\Program Files\Attentive Antivirus virus\RandomFileName.exe”
Tip: Before deleting the malicious Startup entries, open Windows Explorer to find and delete manually the malicious folders and files from your computer. (e.g. RandomFolderName, RandomFileName.exe).
5. Close “CCleaner” and proceed to next step.
Step 4. Delete “Malware Protection” hidden folder/files
1. Open Windows Control Panel: “Start” > “Control Panel”
2. Change the control panel view from “Category” to “Small icons”.
3. Double-click to open “Folder Options”.
4. Select “View” tab and in the “Advanced Settings” list, check to enable the “Show hidden files folders and drives” option.
5. Click “OK” when finish.
6. Open Windows explorer and delete the “defender.exe” file from the following location:
- Windows XP: C:\Documents and Settings\<YourUserName>\Application Data
- Windows 8, 7, Vista : C:\Users\<YourUserName>\AppData\Roaming
Step 5. Clean your computer from remaining malicious threats.
Download and install one of the most reliable FREE anti malware programs today to clean your computer from remaining malicious threats. If you want to stay constantly protected from malware threats, existing and future ones, we recommend that you install Malwarebytes Anti-Malware PRO:
Malwarebytes™ Protection
Removes Spyware, Adware & Malware.
Start Your Free Download Now!
1. Run "Malwarebytes Anti-Malware" and allow the program to update to it's latest version and malicious database if needed.
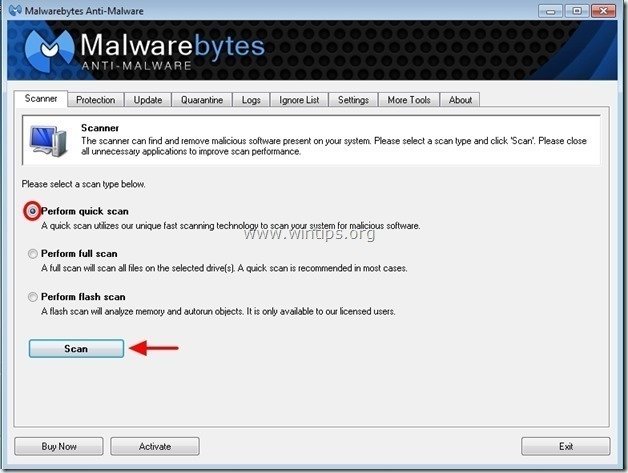
2. When the "Malwarebytes Anti-Malware" main window appears on your screen, choose the "Perform quick scan" option and then press "Scan" button and let the program scan your system for threats.
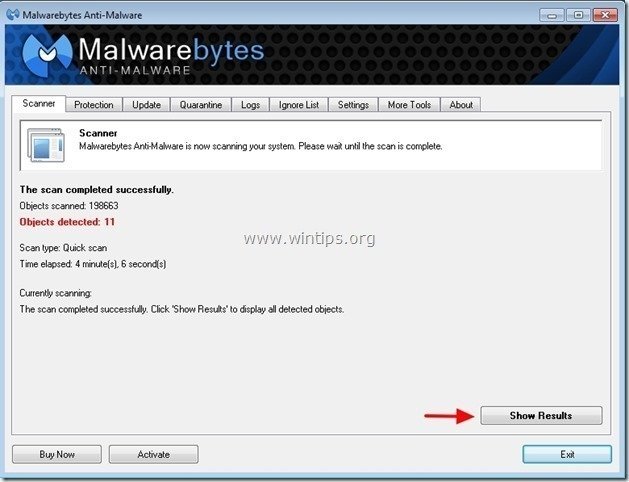
3. When the scanning is completed, press “OK” to close the information message and then press the "Show results" button to view and remove the malicious threats found.
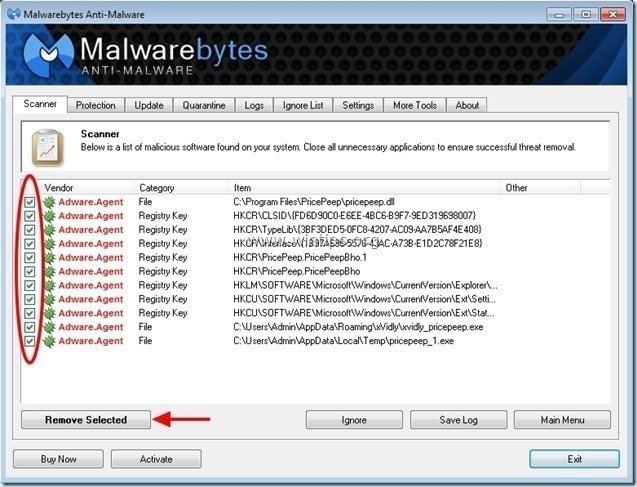
4. At the "Show Results" window check – using your mouse's left button- all the infected objects and then choose the "Remove Selected" option and let the program remove the selected threats.
5. When the removal of infected objects process is complete, "Restart your system to remove all active threats properly"
6. Continue to the next step.


![safe-mode-with-networking_thumb1_thu[2]_thumb safe-mode-with-networking_thumb1_thu[2]_thumb](https://www.wintips.org/wp-content/uploads/2013/12/safe-mode-with-networking_thumb1_thu2_thumb_thumb.jpg)